



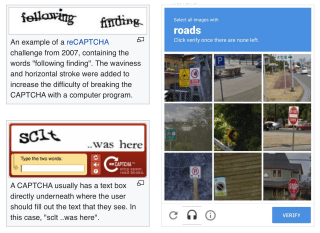
Chances are that you've encountered a CAPTCHA in the wild: they protect web forms by asking you to type over weirdly rendered characters or by asking you to select photos containing a particular thing. Why are they used and is there a user friendly alternative?
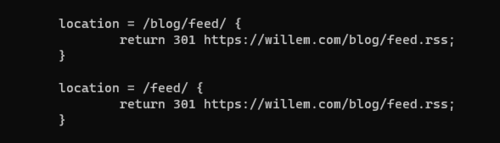
Writing for my blog has been a lot of fun, I receive messages from all of the world about the things I like. Traffic is growing, every month more readers are finding their way to my blog. This week I received a request to support RSS feeds on my blog. I wondered, are RSS feeds still relevant today?
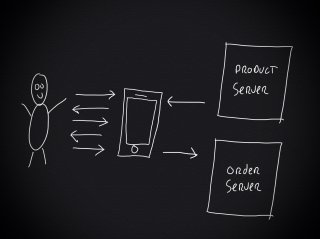
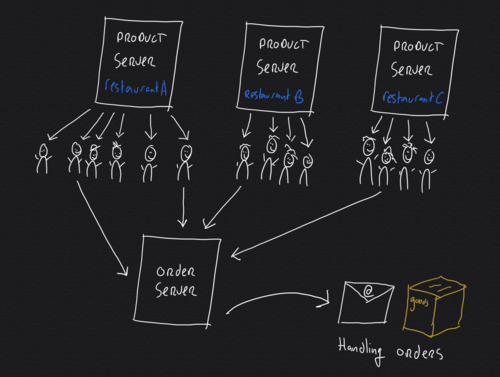
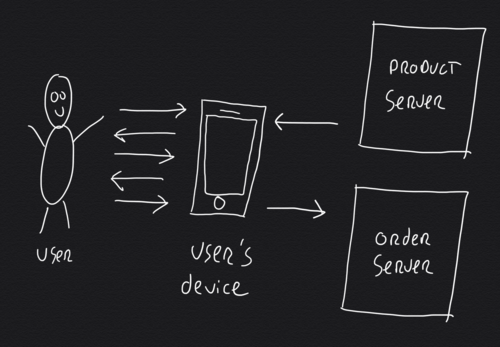
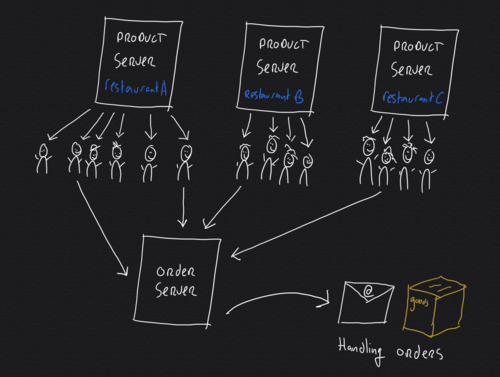
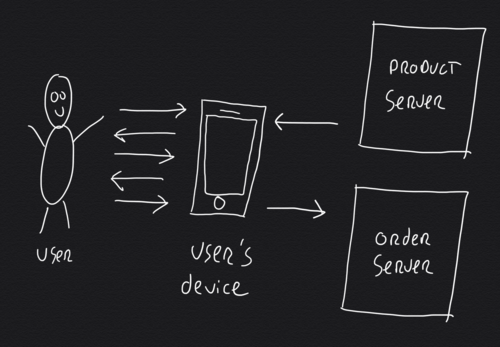
As part of the online food ordering app I'm building, I needed to design a scalable backend infrastructure that could handle lots of concurrent users. Scalability is considered a hard problem to tackle. Often it's presented like it's something magical, done by million dollar companies using secret tools. But, there is no such thing as magic, or is there?

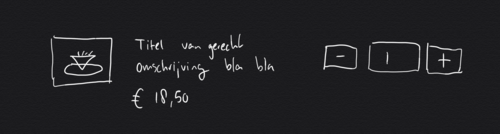
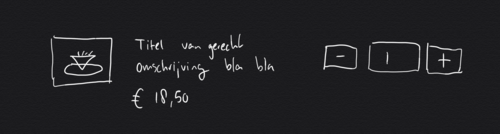
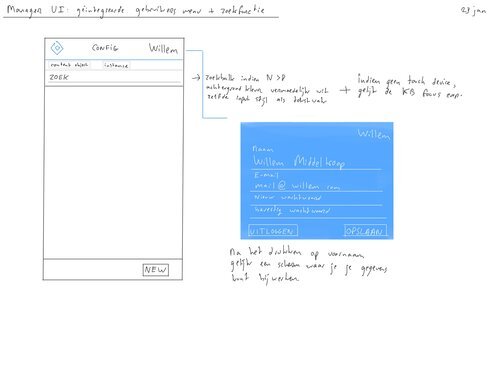
Online ordering pages are more important than ever before. The COVID-19 virus, the resulting lockdowns and the social distancing rules have emphasised the need for a well-designed webshop user interface. This is surprisingly hard to get right!

You probably use the world's most famous search engine to find things everyday, but you might not know about some of its advanced search operators. You can use these special search phrases to find things that are otherwise burried in the search results. Read along for a comprehensive list of advanced Google search operators.

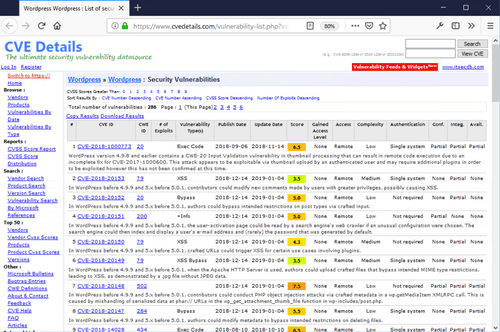
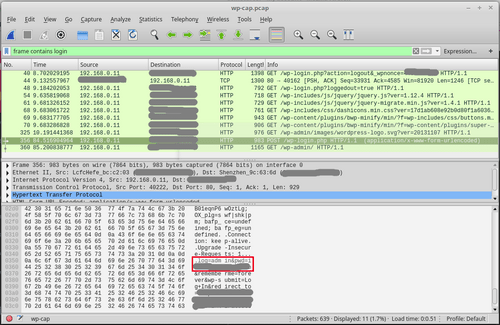
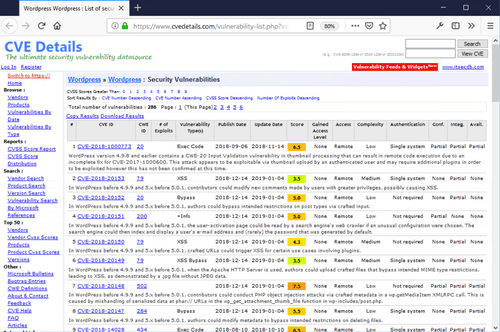
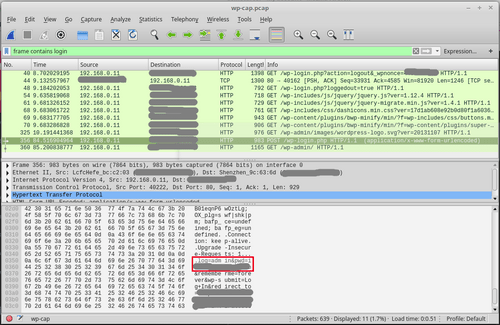
A lot of people use WordPress to manage their website, therefore it's no surprise people ask me to have a look at their site's security. As ethical hacker, I encounter WordPress in different shapes, sizes and states. Some of them are really badly protected against hacks. Prevent your site from being hacked using these 10 practical tips.
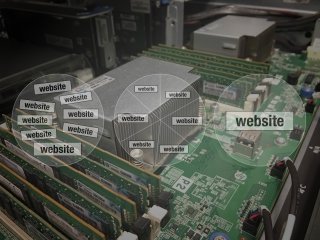
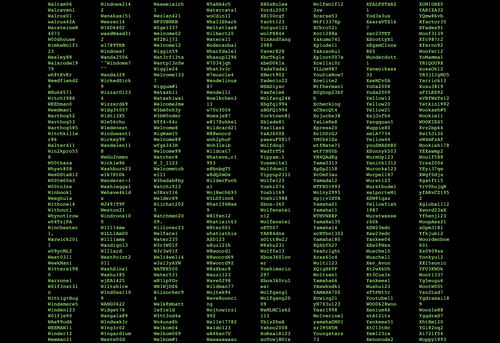
People pay me to hack them, provided I'll explain how it was done, so future hacks can be prevented. As security consultant, I scan for weaknesses in my clients' apps, webshops and websites. Very often a hack starts by exploiting a security hole that is visible remotely. Read along to learn how hackers find security holes and what you can do to secure them.
One way to make your website faster is to make it smaller. Not with tiny fonts, but with less bytes! More than half the weight of an average website is because of images. Yet very few people optimise their images for the web and performance, time to find out how much bytes you can safe!

This month I have been working on website statistics, tracking traffic using different technologies. Some of my customers use Google Analytics, others use AWStats, and some use both. Which is better is often debated, but few people really understand the differences. Time to shed some light on the magic of web statistics.

Today I called my provider to quit my office's ADSL internet subscription, I don't need it anymore. I have turned off my local area network and switched my workflow onto mobile internet only. The simplicity and savings actually surprised me so much, that I made blog post for it.
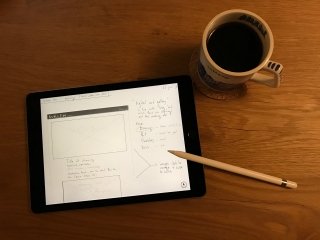
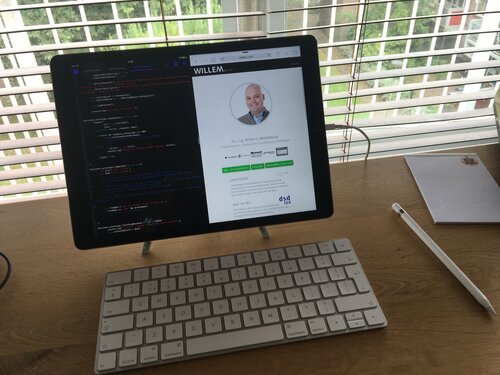
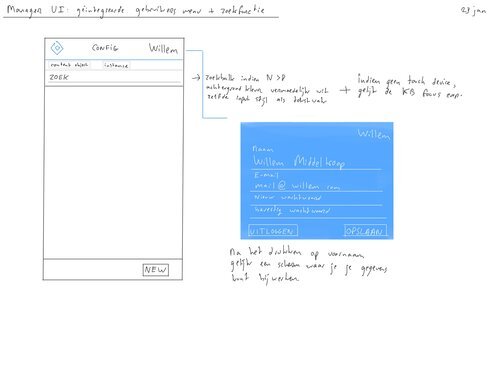
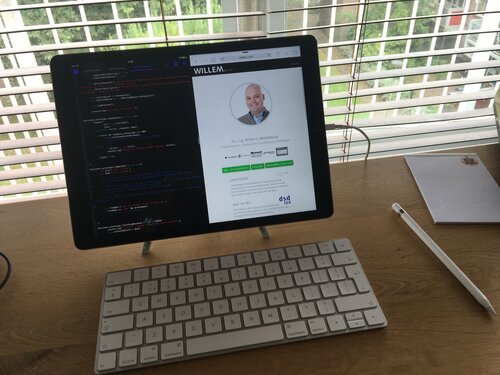
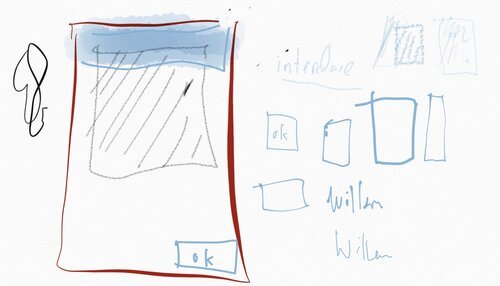
I wanted see if I can find something better than my old fashioned pencil and paper that I use for designing software as professional developer. I knew iPad Pro from my test last summer, figuring out if it could replace my primary development machine. While it may not be able to completely replace my thrustworthy ThinkPad, it turned out to be a totally different story when it comes to paper.

The lack of physical clutter, distracting branding, or blinking LED's makes the iPad Pro a textbook example of minimal design. My despiction of distraction explains my interest in using the iPad Pro as only computer to test if it is up to the task. Is Apple's latest effort on iOS enough to enable it to do serious development work?

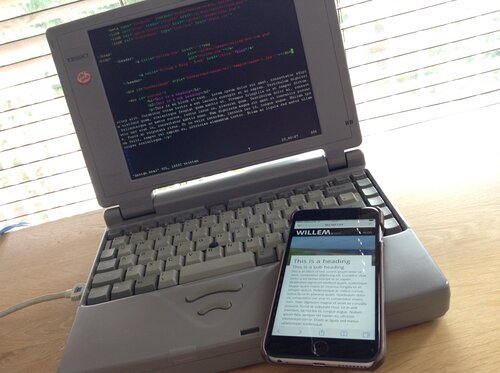
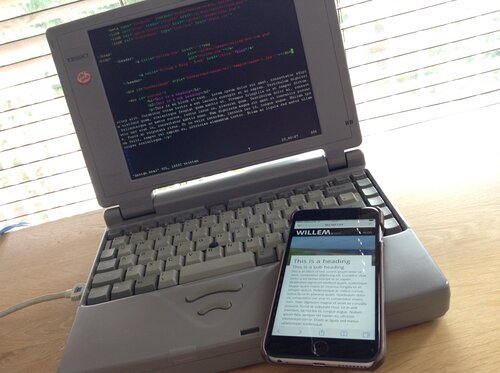
One must be a bit crazy to come up with the idea to build a blog (as in: actual programming) on an old 486 laptop with just 16MB RAM. I happen to be that crazy: I took my very first laptop from the 90s and decided to find out if it was possible to turn it into a development machine.